In the realm of cybersecurity, encryption plays a pivotal role in safeguarding sensitive data from falling into the wrong hands. BitLocker, Microsoft’s full-disk encryption solution, has long been regarded as a robust and reliable tool to protect data on Windows systems. However, recent rumors have emerged suggesting that the seemingly impenetrable BitLocker encryption can be broken using a rather unexpected device – the Raspberry Pi Pico microcontroller.
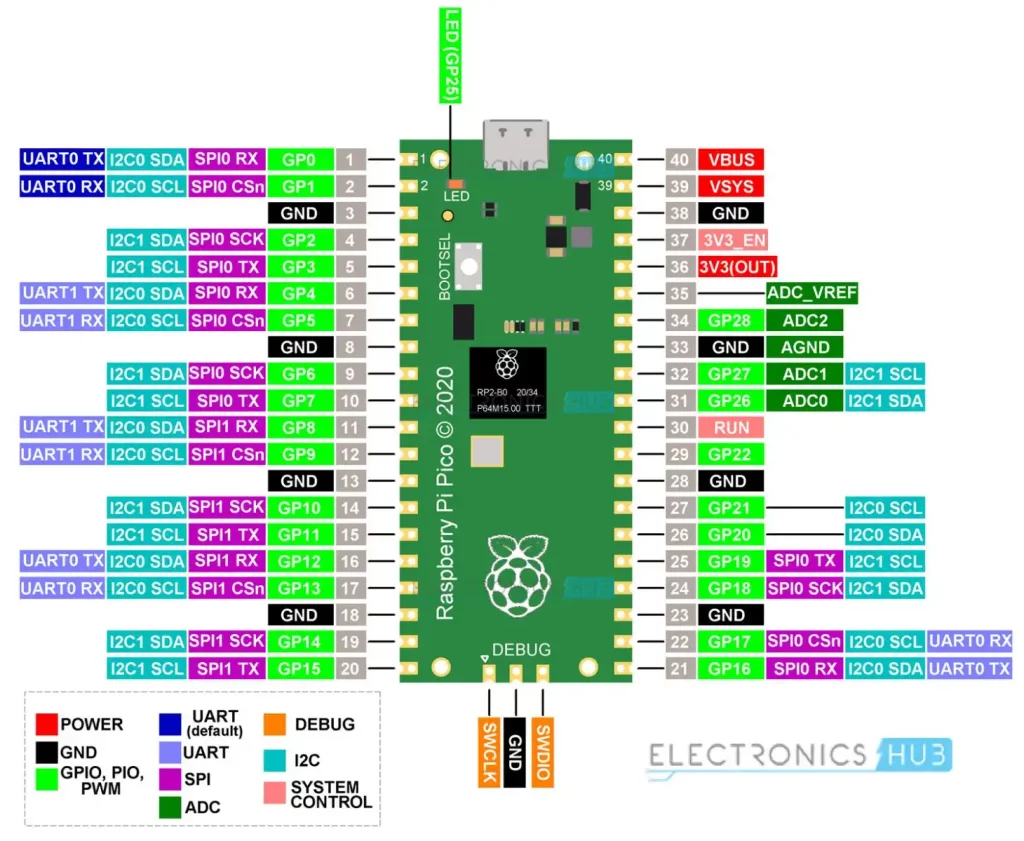
Before delving into the potential implications of this rumor, let’s take a moment to understand what the Raspberry Pi Pico is. Developed by the Raspberry Pi Foundation, the Pico is a tiny yet powerful microcontroller board that has garnered attention for its versatility and affordability. Its programmability and GPIO (General Purpose Input/Output) capabilities make it a favorite amongst hobbyists and professionals alike.
According to these rumors, a group of security researchers has discovered a vulnerability in the BitLocker encryption system that allows them to bypass its security measures using a modified Raspberry Pi Pico. This alleged breakthrough has sent shockwaves through the cybersecurity community, raising questions about the effectiveness of BitLocker and the overall integrity of modern encryption systems.
While specific details about the vulnerability remain scarce, it is believed that the Raspberry Pi Pico is being utilized as a hardware-based attack vector to exploit weaknesses in BitLocker’s encryption algorithms. The device is said to be able to intercept and manipulate the encryption keys during the boot process, effectively rendering the encryption useless and granting unauthorized access to the encrypted data.
If these rumors hold true, the implications for data security could be significant. BitLocker has long been trusted by individuals and organizations alike to protect sensitive information from unauthorized access. A successful attack on BitLocker’s encryption would undermine the faith placed in this widely adopted security solution and raise concerns about the vulnerability of other encryption systems.
It is important to note that at this stage, these rumors are just that – rumors. No concrete evidence or official statements have been released to substantiate these claims. However, the potential ramifications of such a vulnerability underscore the importance of continuous research and development in encryption technologies.
If these rumors are proven to be true, it is crucial for Microsoft to address the vulnerability promptly and release a security patch to mitigate the risk. Additionally, users should ensure that their systems are up to date with the latest security updates and practice good security hygiene by implementing multi-factor authentication and regularly backing up important data.
The possibility of BitLocker encryption being compromised using the Raspberry Pi Pico has sent shockwaves through the cybersecurity community. While these rumors should be approached with caution until concrete evidence emerges, they serve as a reminder that even the most robust security measures may have vulnerabilities that need to be addressed. As technology continues to evolve, it is imperative that encryption systems adapt and strengthen their defenses to stay one step ahead of potential threats.